Oct 25, 2025·8 min
Build a Web App to Track Feature Ownership Across Teams
Learn how to design and build a web app that maps product features to owners across teams, with roles, workflows, integrations, and reporting.
Learn how to design and build a web app that maps product features to owners across teams, with roles, workflows, integrations, and reporting.
Feature ownership tracking solves a specific kind of confusion: when something changes, breaks, or needs a decision, nobody is sure who is accountable—and the “right” person depends on context.
Define ownership as a set of responsibilities, not a name in a field. In many organizations, a single feature has multiple owners:
Decide whether your app supports one primary owner plus secondary roles, or a role-based model (e.g., Product Owner, Tech Owner, Support Lead). If you already use RACI terminology, state how it maps (Responsible/Accountable/Consulted/Informed).
List the groups who will rely on the system day-to-day:
Also note occasional users (execs, QA, security). Their questions will shape reporting, workflows, and permissions.
Write these as acceptance tests. Common must-answer questions include:
Be clear about the unit you’re tracking:
If you include multiple asset types, define relationships (a feature depends on a service; a runbook supports a feature) so ownership doesn’t fragment.
Pick measurable outcomes, such as:
A feature ownership tracker only works if it answers a few questions quickly and reliably. Write requirements in terms of everyday actions—what someone needs to do in 30 seconds, under pressure, during a release or incident.
The MVP should support a small set of workflows end-to-end:
If the app can’t do these four reliably, extra features won’t save it.
To avoid turning this into “yet another planning tool,” explicitly exclude:
Decide what “accurate” means:
For an MVP, a common compromise is: people/teams synced nightly, ownership updated manually, with a visible “last confirmed” date.
Define what ships now versus later to prevent scope creep.
MVP: search, feature page, owner fields, change request + approval, basic audit history, and exports.
Later: advanced reporting dashboards, RACI views across initiatives, Slack/Teams workflows, automated stale-data detection, and multi-source reconciliation.
The goal of v1 is a trustworthy directory of accountability—not a perfect mirror of every system you use.
If you want to validate this quickly before committing to a full build pipeline, a vibe-coding platform like Koder.ai can help you prototype the core flows (search → feature page → change request → approval) via chat, then iterate with stakeholders using snapshots and rollback.
A feature ownership app only works if everyone agrees what a “feature” is. Start by picking a consistent definition and writing it down in the UI where people will see it.
Choose one of these and stick to it:
Teams can still discuss these differently, but the catalog should represent one level. A practical choice is user-visible features, because they map cleanly to tickets, release notes, and support escalations.
Names change; identifiers should not. Give every feature a stable key and a readable URL slug.
FEAT-1427 or REP-EXPORT).export-to-csv).Define naming rules early (sentence case, no internal abbreviations, include product area prefix, etc.). This prevents “CSV Export”, “Export CSV”, and “Data Export” from becoming three different records.
A good taxonomy is just enough structure to filter and group ownership. Common fields:
Keep values curated (dropdowns) so reporting stays clean.
Ownership is rarely a single person. Define owner roles explicitly:
If you already use a RACI model, reflect it directly so people don’t have to translate concepts.
A clear data model is what makes ownership searchable, reportable, and trustworthy over time. The goal isn’t to model every org nuance—it’s to capture “who owns what, since when, until when, and what changed.”
Start with a small set of first-class entities:
Model ownership as records with dates, not as a single mutable field on the Feature. Each OwnershipAssignment should include:
feature_idowner_type + owner_id (Team or Person)role (e.g., DRI, backup, technical owner)start_date and optional end_datehandover_notes (what the next owner needs to know)This structure supports clean handovers: ending one assignment and starting another preserves history and prevents silent ownership changes.
Add an AuditLog (or ChangeLog) that captures every important write:
Keep the audit log append-only. It’s essential for accountability, reviews, and answering “when did ownership switch?”
If you’ll import teams or users, store stable mapping fields:
external_system (System)external_id (string)Do this for Team and Person at minimum, and optionally for Feature if it mirrors Jira epics or a product catalog. External IDs let you sync without duplicate records or broken links when names change.
Getting access control right is what keeps a feature ownership app trustworthy. If anyone can change an owner, people stop relying on it. If it’s too locked down, teams work around it in spreadsheets.
Start with the login method your organization already uses:
A practical rule: if HR can disable an account in one place, your app should follow that same switch.
Use a small set of roles that map to real work:
Role alone isn’t enough—you need scope. Common scoping options:
For example: an Editor can edit ownership only for features within “Billing,” while Approvers can approve changes across “Finance Products.”
When a user tries to edit something they can’t, don’t just show an error. Provide a Request access action that:
Even if you start with a simple email or inbox workflow, a clear path prevents shadow documents and keeps ownership data centralized.
A feature ownership app succeeds when people can answer two questions in seconds: “Who owns this?” and “What should I do next?” Your information architecture should center on a small set of pages with predictable navigation and strong search.
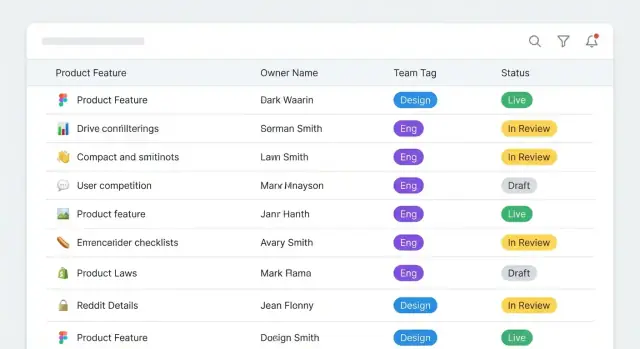
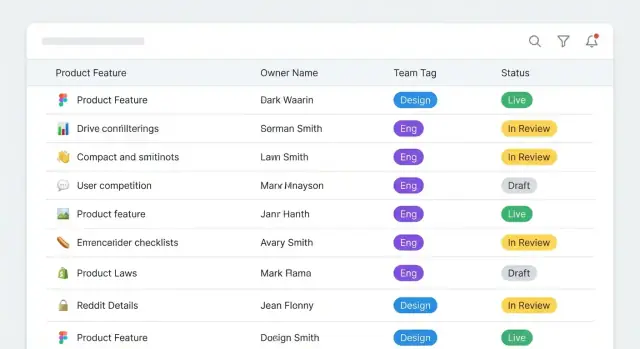
Feature List is the default landing page. It’s where most users start, so optimize it for scanning and narrowing down. Show a compact row layout with: feature name, product area, current owner (team + primary person), status, and “last updated.”
Feature Details is the source of truth. It should clearly separate ownership from description, so updates don’t feel risky. Put the ownership panel at the top with plain labels like Accountable, Primary contact, Backup contact, and Escalation path.
Team Page answers “What does this team own?” Include the team’s channels (Slack/email), on-call info (if relevant), and a list of owned features.
Person Page answers “What is this person responsible for?” It should show active ownership assignments and how to reach them.
Make search always available (header search is ideal) and fast enough to feel instant. Pair it with filters that match how people think:
On the list and details pages, make ownership information highly scannable: consistent badges, clear contact methods, and a one-click “Copy escalation message” or “Email owner” action.
Use a single, consistent edit flow across pages:
This keeps edits safe, reduces back-and-forth, and encourages people to keep ownership data current.
Ownership data stays accurate only if changing it is easier than working around it. Treat updates like small, trackable requests—so people can propose changes quickly, and leaders can trust what they see.
Instead of editing ownership fields directly, route most edits through a change request form. Each request should capture:
Scheduled effective dates are useful for reorganizations: the new owner shows up automatically on the date, while the audit trail preserves who owned it before.
Not every change needs a meeting. Add lightweight approvals only when risk is higher, for example:
A simple rule engine can decide: auto-approve low-risk edits, but require 1–2 approvers for sensitive ones (e.g., current owner + receiving team lead). Keep approval screens focused: proposed values, diff view, reason, and effective date.
When ownership moves between teams, trigger a handover checklist before the change becomes effective. Include structured fields such as:
This turns ownership into something operational, not just a name.
Define conflicts explicitly and flag them where people work:
Surface conflicts on the feature page and in a dashboard view (see /blog/reporting-dashboards), so teams can clean up issues before they become incidents.
A feature ownership app only works if people notice when something needs attention. The goal is to prompt action without spamming everyone.
Start with a small set of high-signal events:
For each event, decide who gets notified: the new owner, previous owner, the feature’s team lead, and optionally a program/product operations inbox.
Real-time alerts are great for approvals and owner changes, but reminders can quickly become background noise. Offer digests such as:
Make digests configurable per user and per team, with sensible defaults. A simple “snooze for 7 days” option also prevents repeated pings during busy periods.
Unassigned ownership is where projects stall. Create an escalation path that’s predictable and visible:
Keep escalation rules transparent in the UI (e.g., “Escalates to X after 5 business days”) so notifications don’t feel arbitrary.
Don’t bake in a single chat tool. Provide a generic webhook notification target so teams can route alerts to Slack, Microsoft Teams, email gateways, or incident tools.
At minimum, include: event type, feature ID/name, old/new owner, timestamps, and a deep link back to the record (e.g., /features/123).
A feature ownership app only stays useful if it reflects reality. The fastest way to lose confidence is stale data: a team rename in HR, a feature moved in the issue tracker, or an owner who left the company. Treat integrations as a core part of the product, not an afterthought.
Start with a small set of high-signal sources:
Keep the first iteration simple: store IDs and URLs, and display them consistently. You can add deeper synchronization after teams rely on the app.
Decide whether your app is:
A practical middle ground is read-only sync plus “propose changes” workflows that notify the right owner to update the source.
Even with integrations, you’ll need bulk operations:
Make CSV templates strict (required columns, valid team/user IDs) and provide error reports that non-technical users can fix.
Every synced field should show:
If a sync fails, show what’s impacted and what still might be correct. This transparency keeps teams using the app instead of reverting to side spreadsheets.
Reporting is where your app stops being a database and becomes a daily tool. The goal is to answer the most common ownership questions in seconds: Who owns this? Is it current? What’s risky right now?
Start with a small set of dashboards that highlight operational gaps rather than vanity metrics:
Each card should be clickable into a filtered list, with an obvious next step (“Assign owner”, “Request confirmation”, “Escalate”). A simple mental model: treat dashboards as queues.
An ownership matrix view helps cross-team groups (support, SRE, release managers) see patterns at a glance.
Make it a grid: rows = features, columns = teams, cell = relationship (Owner, Contributor, Consulted, Informed). Keep it readable:
Not everyone needs to use the app to benefit from it. Add a one-click export that produces a RACI-style table for a chosen scope (product area, release, or tag). Provide:
Keep definitions consistent across the UI and exports so people don’t argue about what “Accountable” means.
Saved views prevent dashboard sprawl. Offer curated defaults plus personal/team saves:
Ownership changes have process impact, so reporting should include trust signals:
Link these views from feature pages and admin screens (see /blog/access-control for role design patterns).
A feature-ownership tracker succeeds when it’s easy to ship, safe to change, and clearly owned itself. Treat implementation, deployment, and governance as part of the product—not afterthoughts.
Start with what your team can comfortably support.
If you want fast delivery and simple operations, a server-rendered app (e.g., Rails/Django/Laravel) with a relational database is often enough. If you already have strong front-end expertise and need highly interactive workflows (bulk edits, inline approvals), a SPA (React/Vue) plus an API can fit—just budget time for API versioning and error handling.
Either way, use a relational DB (Postgres/MySQL) for ownership history and constraints (e.g., “one primary owner per feature”), and keep the audit trail immutable.
If you prefer to accelerate delivery without rebuilding a full pipeline upfront, Koder.ai can generate a working React UI and Go/PostgreSQL backend from a chat-driven spec, then let you export the source code when you’re ready to bring it fully in-house.
Set up three environments early: dev, staging, production. Staging should mirror production permissions and integrations so approvals and sync jobs behave the same.
Plan these basics up front:
If you maintain internal docs, add a short runbook under /docs/runbook with “how to deploy,” “how to restore,” and “where to look when sync fails.”
Prioritize tests where mistakes create real damage:
Assign clear maintainers for the taxonomy (teams, domains, feature naming rules). Set a review cadence (monthly or quarterly) to clean up duplicates and stale ownership.
Finally, define a definition of done for ownership, such as: named primary owner, backup owner, last reviewed date, and a link to the team channel or on-call rotation.
Feature ownership is a defined set of responsibilities for a feature, often split by role:
Write this definition into the app UI so “owner” doesn’t become an ambiguous name field.
Most teams need answers to a few high-pressure questions:
Design the MVP to answer these in under a minute from search.
A practical MVP is a “trustworthy directory of accountability,” not a planning tool. Include:
Defer dashboards, deep automations, and chat workflows until usage is stable.
Pick one level and enforce it:
If you also track services/docs/runbooks, define relationships (e.g., “Feature depends on Service”) so ownership doesn’t fragment across disconnected records.
Use stable identifiers that don’t change when names do:
FEAT-1427)Also add naming conventions (case, prefixes, banned abbreviations) to prevent duplicates like “CSV Export” vs “Export CSV.”
Model ownership as time-bounded records (not a single mutable field):
feature_id, owner_id, rolestart_date and optional end_datehandover_notesThis lets you end one assignment and start another cleanly, preserves history, and supports scheduled handovers during reorganizations.
An append-only audit log keeps the system trustworthy. Capture:
It’s how you answer “when did ownership switch?” during incidents, reviews, and compliance checks.
Keep roles simple, then add scope:
Also add a “Request access” path when users hit a permission wall so they don’t create shadow spreadsheets. For more patterns, see /blog/access-control.
Treat changes as requests with an effective date and reason:
For cross-team transfers, require a handover checklist (docs, runbooks, risks) before the change becomes effective.
Use high-signal notifications with optional digests:
Make escalation rules explicit (e.g., “escalates after 5 business days”) and integrate via webhooks so teams can route alerts to their tools without hard-coding a single chat platform.