Jun 16, 2025·8 min
How to Build a Web App for Project Dependency Management
Plan, design, and ship a web app that tracks cross-functional project dependencies, owners, risks, and timelines with clear workflows, alerts, and reporting.
Clarify the Use Case and Success Metrics
Before you design screens or pick a tech stack, get precise about the problem you’re solving. A dependency app fails when it becomes “another place to update,” while the real pain—surprises and late handoffs between teams—continues.
Define the core problem
Start with a simple statement you can repeat in every meeting:
Cross-functional dependencies are causing delays and last‑minute surprises because ownership, timing, and status are unclear.
Make it specific to your organization: which teams are most affected, what types of work get blocked, and where you currently lose time (handoffs, approvals, deliverables, data access, etc.).
Identify target users (and what they need)
List the primary users and how they will use the app:
- Project managers: need a reliable view of upcoming blockers and what to escalate.
- Team leads: need clarity on what their team owes, by when, and tradeoffs.
- Exec sponsors: need a high-level risk view and accountability.
- Individual contributors (ICs): need actionable requests, context, and due dates.
Capture the top jobs-to-be-done
Keep the “jobs” tight and testable:
- Discover dependencies early (during planning, not during delivery).
- Create dependency requests with clear scope and dates.
- Validate (accept/reject) with negotiated timelines.
- Track progress and changes over time.
- Escalate when risk increases or commitments slip.
Decide what “dependency” means here
Write a one-paragraph definition. Examples: a handoff (Team A provides data), an approval (Legal sign-off), or a deliverable (Design spec). This definition becomes your data model and workflow backbone.
Set success metrics
Choose a small set of measurable outcomes:
- Fewer active blockers per project (or fewer “late discovered” dependencies).
- Faster average time from request → acceptance → delivery.
- Better predictability (fewer date slips, higher on-time delivery rate).
If you can’t measure it, you can’t prove the app is improving execution.
Map Stakeholders and Current Workflow
Before you design screens or databases, get clear on who participates in dependencies and how work moves between them. Cross-functional dependency management fails less from bad tooling and more from mismatched expectations: “Who owns it?”, “What does done mean?”, “Where do we see status?”
Find where dependency data lives today
Dependency information is usually scattered. Do a quick inventory and capture examples (real screenshots or links) of:
- Spreadsheets tracking “asks” and dates
- Jira/Asana/Trello tickets and epics
- Docs and meeting notes (Google Docs/Notion/Confluence)
- Slack/Teams threads where decisions and promises happen
This tells you what fields people already rely on (due dates, links, priority) and what’s missing (clear owner, acceptance criteria, status).
Map the workflow end-to-end
Write the current flow in plain language, typically:
request → accept → deliver → verify
For each step, note:
- Who triggers it (role/team, not a person)
- What information is required to proceed
- Where it’s recorded today
- What “complete” means (and who signs off)
Spot failure points and rank pain
Look for patterns like unclear owners, missing due dates, “silent” status, or dependencies discovered late. Ask stakeholders to rank the most painful scenarios (e.g., “accepted but never delivered” vs. “delivered but not verified”). Optimize the top 1–2 first.
Anchor the build with user stories
Write 5–8 user stories that reflect reality, such as:
- “As a requesting PM, I can submit a dependency with a needed-by date and context so the owning team can evaluate it.”
- “As an owning lead, I can accept/reject with a commitment date so expectations are explicit.”
- “As a stakeholder, I can see status at a glance so I don’t chase updates in meetings.”
These stories become your scope guardrails when feature requests start piling up.
Design the Dependency Data Model
A dependency app succeeds or fails on whether everyone trusts the data. The goal of your data model is to capture who needs what, from whom, by when, and to keep a clean record of how commitments change over time.
Core dependency record
Start with a single “Dependency” entity that is readable on its own:
- Title: short, specific (e.g., “Provide legal review for updated checkout copy”)
- Description: context, acceptance criteria, links
- Type: a controlled list (e.g., review, delivery, approval, data access)
- Owning team: the team expected to deliver
- Requester: person or team asking for it
Keep these fields mandatory where possible; optional fields tend to become empty fields.
Dates and commitments
Dependencies are really about time, so store dates explicitly and separately:
- Requested by (the requester’s need-by date)
- Committed by (the owning team’s promise date)
- Delivered on (the actual completion date)
- Review window (a start/end range for validation or sign-off)
This separation prevents arguments later (“requested” is not the same as “committed”).
Status and relationships
Use a simple, shared status model: proposed → pending → accepted → delivered, with exceptions like at risk and rejected.
Model relationships as one-to-many links so each dependency can connect to:
- Projects (one dependency may impact multiple initiatives)
- Milestones (tie it to a specific delivery checkpoint)
- Tickets (e.g., Jira issues for execution)
Auditability and trust
Make changes traceable with:
- Created/updated by
- Change history (field-level updates over time)
- Comments (decision notes, clarifications, approvals)
If you get the audit trail right early, you’ll avoid “he said/she said” debates and make handoffs smoother.
Model Projects, Milestones, and Team Ownership
A dependency app only works if everyone agrees on what a “project” is, what a “milestone” is, and who is accountable when things slip. Keep the model simple enough that teams will actually maintain it.
Projects and milestones: pick the right granularity
Track projects at the level people plan and report on—usually an initiative that lasts weeks to months and has a clear outcome. Avoid creating a project for every ticket; that belongs in delivery tools.
Milestones should be few, meaningful checkpoints that can unblock others (e.g., “API contract approved,” “Beta launch,” “Security review complete”). If milestones get too detailed, updates become a chore and data quality drops.
A practical rule: projects should have 3–8 milestones, each with an owner, target date, and status. If you need more, consider making the project smaller.
Team directory: make ownership discoverable
Dependencies fail when people don’t know who to talk to. Add a lightweight team directory that supports:
- Team name and function (e.g., Payments, Data Platform, Legal)
- Primary contact (person) and backup/on-call contact
- Preferred channel (email, Slack handle, ticket queue)
This directory should be usable even by non-technical partners, so keep fields human-readable and searchable.
Ownership rules: accountability without confusion
Decide upfront whether you allow shared ownership. For dependencies, the cleanest rule is:
- Single accountable owner per milestone/dependency (one person)
- Optional collaborators (many people)
If two teams truly share responsibility, model it as two milestones (or two dependencies) with a clear handoff, instead of “co-owned” items that no one drives.
Cross-project dependencies and program rollups
Represent dependencies as links between a requesting project/milestone and a delivering project/milestone, with a direction (“A needs B”). This enables program views later: you can roll up by initiative, quarter, or portfolio without changing how teams work day to day.
Tagging strategy that stays useful
Tags help slice reporting without forcing a new hierarchy. Start with a small, controlled set:
- Product area
- Quarter (or target release window)
- Initiative/program name
- Priority (e.g., P0–P3)
Prefer dropdowns over free text for core tags to avoid “Payments,” “payments,” and “Paymnts” becoming three different categories.
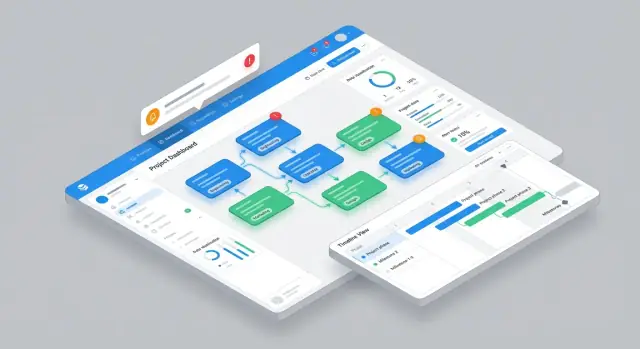
Plan the Core UI and Navigation
A dependency management app succeeds when people can answer two questions in seconds: “What do I owe?” and “What’s blocking me?” Design navigation around those jobs-to-be-done, not around database objects.
Primary views that match real work
Start with four core views, each optimized for a different moment in the week:
- Dependency list for triage and sorting (best for daily check-ins)
- Dependency graph to understand upstream/downstream impact at a glance
- Timeline to spot date collisions and slipping handoffs
- Team inbox as the default landing page for contributors (“requests waiting on me”)
Keep global navigation minimal (e.g., Inbox, Dependencies, Timeline, Reports), and let users jump between views without losing their filters.
Fast creation without sacrificing clarity
Make creating a dependency feel as quick as sending a message. Provide templates (e.g., “API contract,” “Design review,” “Data export”) and a Quick Add drawer.
Require only what’s necessary to route work correctly: requesting team, owning team, due date, short description, and status. Everything else can be optional or progressively disclosed.
Filtering, search, and saved views
People will live in filters. Support search and filters by team, date range, risk, status, project, plus “assigned to me.” Allow users to save common combinations (“My Q1 launches,” “High risk this month”).
Accessibility and empty-state guidance
Use color-safe risk indicators (icon + label, not color alone) and ensure full keyboard navigation for creating, filtering, and updating statuses.
Empty states should teach. When a list is empty, show a short example of a strong dependency:
“Payments team: provide sandbox API keys for Checkout v2 by Mar 14; needed for mobile QA start.”
That kind of guidance improves data quality without adding process.
Build Workflows: Request, Accept, Deliver, Close
Prototype the Dependency App
Turn your dependency workflow into a working web app by describing screens and states in chat.
A dependency tool succeeds when it mirrors how teams actually collaborate—without forcing people into long status meetings. Design the workflow around a small set of states that everyone can recognize, and make every state change answer one question: “What happens next, and who owns it?”
Dependency request flow: create → route → acceptance
Start with a guided “Create dependency” form that captures the minimum needed to act: requesting project, needed outcome, target date, and impact if missed. Then automatically route it to the owning team based on a simple rule (service/component owner, team directory, or manually selected owner).
Acceptance should be explicit: the owning team either accepts, rejects, or requests clarification. Avoid “soft” acceptance—make it a button that creates accountability and timestamps the decision.
Acceptance criteria: definition of done and sign-off
When accepting, require a lightweight definition of done: deliverables (e.g., API endpoint, spec review, data export), acceptance test or verification step, and the sign-off owner on the requesting side.
This prevents the common failure mode where a dependency is “delivered” but not usable.
Change management: dates, scope, reassignments
Changes are normal; surprises are not. Every change should:
- record what changed (date, scope, owner)
- require a short reason
- notify both teams
- keep a visible history so no one debates “who said what”
Escalation path: at-risk flags and SLAs
Give users a clear at-risk flag with escalation levels (e.g., Team Lead → Program Lead → Exec Sponsor) and optional SLA expectations (response in X days, update every Y days). Escalation should be a workflow action, not an angry message thread.
Closure flow: evidence, verification, retrospective notes
Close a dependency only after two steps: delivery evidence (link, attachment, or note) and verification by the requester (or auto-close after a defined window). Capture a short retrospective field (“what blocked us?”) to improve future planning without running a full postmortem.
Add Roles, Permissions, and Auditability
Dependency management breaks down quickly when people aren’t sure who can commit, who can edit, and who changed what. A clear permission model prevents accidental date changes, protects sensitive work, and builds trust across teams.
Define role types that match real work
Start with a small set of roles and expand only when you hit real needs:
- Admin: manages workspace settings, integrations, and global permissions
- Program manager: oversees portfolios, sets governance rules, and resolves disputes
- Team lead: owns team-level commitments and approves incoming dependency requests
- Contributor: creates and updates dependencies they’re involved in, adds notes, proposes changes
- Viewer: read-only access for stakeholders who need visibility without edit power
Permissions by object (and by action)
Implement permissions at the object level—dependencies, projects, milestones, comments/notes—and then by action:
- Create/edit dependencies
- Change dependency status (e.g., Proposed → Accepted → Delivered → Closed)
- Edit committed dates vs. suggested dates
- Delete (usually restricted to Admin/Program manager)
A good default is least-privilege: new users should not be able to delete records or override commitments.
Data visibility and sensitive work
Not all projects should be equally visible. Add visibility scopes such as:
- Internal (default): visible to authenticated users in the workspace
- Sensitive: limited to specific teams or a security group
- Team-private notes: keep candid delivery notes visible only to the owning team, while the dependency status remains visible to stakeholders
Approval controls and auditability
Define who can accept/reject requests and who can change committed dates—typically the receiving team lead (or delegate). Make the rule explicit in the UI: “Only the owning team can commit dates.”
Finally, add an audit log for key events: status changes, date edits, ownership changes, permission updates, and deletions (including who, when, and what changed). If you support SSO, pair it with the audit log to make access and accountability clear.
Implement Alerts and Notifications
Set Roles and Rules
Set who can commit dates and track key edits with an audit-friendly history.
Alerts are where a dependency tool either becomes genuinely helpful—or turns into noise everyone learns to ignore. The goal is simple: keep work moving across teams by notifying the right people at the right time, with the right level of urgency.
Start with clear notification triggers
Define the events that matter most for cross-functional dependencies:
- New request created (the receiving team needs to acknowledge it)
- Request accepted / rejected (the requester needs certainty)
- Due date approaching (prevent last-minute surprises)
- Status changes to “at risk” or “blocked” (prompt action and support)
Tie each trigger to an owner and a “next step,” so a notification isn’t just informational—it’s actionable.
Offer channels without forcing them
Support multiple channels:
- In-app notifications for a clean audit trail and easy triage
- Email for people who live in their inbox
- Slack/Teams (if applicable) for fast team visibility
Keep it configurable at the user and team level. A dependency lead might want Slack pings; an exec sponsor might prefer a daily email summary.
Balance real-time alerts with digests
Real-time messages are best for decisions (accept/reject) and escalations. Digests are better for awareness (upcoming due dates, “waiting on” items).
Include settings like: “immediate for assignments,” “daily digest for due dates,” and “weekly summary for health.” This reduces alert fatigue while still keeping dependencies visible.
Get reminder and escalation logic right
Reminders should respect business days, time zones, and quiet hours. For example: send a reminder 3 business days before a due date, and never notify outside 9am–6pm local time.
Escalations should kick in when:
- A request goes unanswered after a defined SLA (e.g., 48 hours)
- A due date slips or a dependency is marked at risk
Escalate to the next responsible layer (team lead, program manager) and include context: what’s blocked, by whom, and what decision is needed.
Plan Integrations and Data Sync
Integrations make a dependency app useful on day one because most teams already track work elsewhere. The goal isn’t to “replace Jira” (or Linear, GitHub, Slack)—it’s to connect dependency decisions to the systems where execution happens.
Integrations worth prioritizing
Start with tools that represent work, time, and communication:
- Jira / Linear for issues, status, assignees, and sprint/iteration context
- GitHub for pull requests, releases, and deployment signals
- Google Calendar for milestone dates, change windows, and key meetings
- Slack for notifications and lightweight approvals
Choose 1–2 to pilot first. Too many integrations early can turn debugging into your main job.
Import strategy: CSV first, then sync
Use a one-time CSV import to bootstrap existing dependencies, projects, and owners. Keep the format opinionated (e.g., dependency title, requester team, provider team, due date, status).
Then add ongoing sync only for the fields that must stay consistent (like external issue status or due date). This reduces surprise changes and makes troubleshooting easier.
Linking vs syncing (and when)
Not every external field should be copied into your database.
- Linking: store the external system’s ID (e.g., Jira issue key) and deep-link to it. Great when the external tool is clearly the source of truth.
- Syncing: store a local copy of select fields (status, due date, assignee) to support reporting, alerts, and audit history—especially if you need “what changed when.”
A practical pattern is: store external IDs always, sync a small set of fields, and allow manual overrides only where your app is the source of truth.
Webhooks + APIs: event-driven sync
Polling is simple but noisy. Prefer webhooks where possible:
- Listen for status changes (e.g., “In Progress” → “Done”)
- Listen for due date changes (often the most important trigger for dependency risk)
When an event arrives, enqueue a background job to fetch the latest record via API and update your dependency object.
Define data ownership boundaries
Write down which system owns each field:
- Jira/Linear owns issue status and assignee
- Your app owns dependency relationship, commitment date, and accept/decline decisions
- Slack owns delivery channel and message history (don’t try to replicate it)
Clear source-of-truth rules prevent “sync wars” and make governance and audits far simpler.
Create Reporting and Health Dashboards
Dashboards are where your dependency app earns trust: leaders stop asking for “one more status slide,” and teams stop chasing updates across chat threads. The goal isn’t a wall of charts—it’s a fast way to answer, “What’s at risk, why, and who owns the next move?”
Define clear health signals
Start with a small set of risk flags that can be computed consistently:
- Overdue: promised date passed and not delivered
- Blocked: marked as blocked, or missing a required input
- Missing owner: no accountable team/person assigned
- Conflicting dates: requester needs it after the provider’s planned delivery (or vice versa)
These signals should be visible both at the dependency level and rolled up to project/program health.
Build meeting-ready views
Create views that match how steering meetings run:
- Upcoming critical dependencies: next 2–4 weeks, sorted by risk and due date
- Team capacity impact: show where incoming requests exceed a team’s available bandwidth (even a simple “low/medium/high load” indicator helps)
- Program rollups: group dependencies by initiative, quarter, or release train so leaders can compare workstreams without manual aggregation
A good default is a single page that answers: “What changed since last week?” (new risks, resolved blockers, date shifts).
Make sharing effortless
Dashboards often need to leave the app. Add exports that preserve context:
- CSV for analysis and filtering
- PDF for steering meetings and approvals
When exporting, include owner, due dates, status, and the latest comment so the file stands on its own. That’s how dashboards replace manual status slides instead of creating another reporting task.
Select a Practical Tech Stack and Architecture
Launch a Pilot Build
Host your pilot app so 2 to 3 teams can try it in real work.
The goal isn’t to pick “the perfect” technology—it’s to choose a stack your team can build and operate confidently while keeping dependency views fast and trustworthy.
Start with a simple, proven shape
A practical baseline is:
- A web app (server-rendered or SPA) for day-to-day use
- A single API (REST or GraphQL) to power the UI and integrations
- A relational database
- Background jobs for notifications, scheduled syncs, and report generation
This keeps the system easy to reason about: user actions are handled synchronously, while slow work (sending alerts, recalculating health metrics) happens asynchronously.
Database: model links like you mean it
Dependency management is heavy on “find all items blocked by X” queries. A relational model works well for this, especially with the right indexes.
At minimum, plan for tables like Projects, Milestones/Deliverables, and Dependencies (from_id, to_id, type, status, due dates, owners). Add indexes for common filters (team, status, due date, project) and for traversals (from_id, to_id). This prevents the app from slowing down as the number of links grows.
Graphs and timelines: pick libraries with performance in mind
Dependency graphs and Gantt-style timelines can get expensive. Choose rendering libraries that support virtualization (render only what’s visible) and incremental updates. Treat “show me everything” views as advanced modes, and default to scoped views (per project, per team, per date range).
Keep views fast: caching and pagination
Paginate lists by default, and cache common computed results (e.g., “blocked count per project”). For graphs, preload just the neighborhood around a selected node, then expand on demand.
Deployment basics you’ll be glad you did
Use separate environments (dev/staging/prod), add monitoring and error tracking, and log audit-relevant events. A dependency app quickly becomes a source of truth—downtime and silent failures cost real coordination time.
A fast path if you’re prototyping
If your main goal is to validate workflows and UI quickly (inbox, acceptance, escalation, dashboards) before committing engineering bandwidth, you can prototype a dependency-management app in a vibe-coding platform like Koder.ai. It lets you iterate through the data model, roles/permissions, and key screens via chat, then export source code when you’re ready to productionize (commonly React on the web, Go + PostgreSQL on the backend). This can be especially useful for a pilot with 2–3 teams where speed of iteration matters more than perfect architecture on day one.
Test, Pilot, and Roll Out Safely
A dependency app only helps if people trust it. That trust is earned through careful testing, a contained pilot, and a rollout that doesn’t disrupt teams mid-delivery.
Test the workflow end-to-end
Start by validating the “happy path”: a team requests a dependency, the owning team accepts, work is delivered, and the dependency is closed with a clear outcome.
Then hit edge cases that often break real usage:
- Reassignments: move ownership to another team and confirm history stays intact
- Rejections: reject with a reason, ensure the requester can revise/resubmit
- Date changes: update milestone dates and verify downstream timelines, SLAs, and reports adjust correctly
Permission and audit checks
Dependency apps tend to fail when permissions are either too strict (people can’t do their job) or too loose (teams lose control).
Test scenarios like:
- A requester can edit their request details, but cannot edit the owning team’s delivery fields
- Only designated owners can accept/commit dates
- Admins can intervene, and every critical change is captured in an audit trail (who/what/when)
Notifications without noise
Alerts should make people act, not tune out.
Verify:
- No duplicate notifications when multiple fields change at once
- Throttling works (e.g., one update summary instead of 10 separate pings)
- Digest emails/Slack summaries include enough context (project, dependency, due date, owner) to act without hunting
Seed demo data for validation
Before involving teams, preload realistic demo projects, milestones, and cross-team dependencies. Good seed data exposes confusing labels, missing statuses, and reporting gaps faster than synthetic test records.
Run a small pilot, then expand
Pilot with 2–3 teams that frequently depend on each other. Set a short window (2–4 weeks), collect feedback weekly, and iterate on:
- Status names and required fields
- Notification rules
- Reporting views (what’s “actionable” vs. “interesting”)
Once the pilot teams say the tool saves time, roll out by grouping teams into waves and publishing a clear “how we work now” page (even a simple internal doc linked from the app’s header) so expectations stay consistent.
FAQ
What should I clarify before building a dependency management app?
Start with a one-sentence problem statement you can repeat: dependencies are causing delays because ownership, timing, and status are unclear. Then pick a small set of measurable outcomes, such as:
- Fewer “late-discovered” dependencies
- Faster request → acceptance → delivery time
- Higher on-time delivery rate (predictability)
If you can’t measure improvement, you can’t justify adoption.
Who are the primary users and what do they need from the app?
Keep it tight and role-based:
- Project managers: need early visibility into blockers and what to escalate
- Team leads: need clear asks, tradeoffs, and commitment dates
- Exec sponsors: need rollups of risk and accountability
- ICs: need actionable requests with context and due dates
Design your default views around “What do I owe?” and “What’s blocking me?” rather than around database objects.
How do I define what a “dependency” is in my organization?
Write a one-paragraph definition and stick to it. Common examples:
- A handoff (Team A provides data/artifacts)
- An approval (Legal/Security sign-off)
- A deliverable (Design spec, API contract)
That definition determines your required fields, your workflow states, and how you report “done.”
What fields should the core dependency record include?
A good minimal record captures who needs what, from whom, by when, plus traceability:
- Title, description (with links), type
- Requester and owning team
- Requested-by date, committed-by date, delivered-on date
- Simple status and a comment/history trail
Avoid optional fields that stay empty; make the routing fields mandatory.
What workflow and status model works best for dependencies?
Use a simple, shared flow and make acceptance explicit:
- Proposed → Pending → Accepted → Delivered (plus Rejected and At risk/Blocked)
Acceptance should be a deliberate action (button + timestamp), not implied in a comment thread. This is what creates accountability and clean reporting.
How should I model projects and milestones without making it too complicated?
Pick granularity people already plan and report on:
- A project should be weeks-to-months with a clear outcome
- A project should typically have 3–8 milestones with owners and target dates
If your milestones become too detailed, updates turn into busywork and data quality drops—push ticket-level detail back into Jira/Linear/etc.
How do I handle roles, permissions, and auditability?
Default to least-privilege and protect commitments:
- Only the owning team lead (or delegate) can accept/reject and commit dates
- Requesters can edit request details, but not override provider commitments
- Track key events in an audit log (status/date/owner/permission changes)
This prevents accidental changes and reduces “who said what” debates.
How do I design notifications so they help instead of creating noise?
Start with a small set of triggers that are genuinely actionable:
- New request created
- Accepted/rejected/needs clarification
- Due date approaching
- Marked at risk/blocked or overdue
Offer real-time alerts for decisions and escalations, but use digests for awareness (daily/weekly). Add throttling to avoid “notification storms.”
What’s the right approach to integrations and data sync with tools like Jira or Slack?
Don’t try to replace execution tools. Use integrations to connect decisions to where work happens:
- Always store the external ID (linking)
- Sync only a small set of fields you need for alerts/reporting (e.g., status, due date)
- Prefer webhooks over polling for status/date changes
Write down source-of-truth rules (e.g., Jira owns issue status; your app owns acceptance and commitment dates).
How should I pilot and roll out the app to earn trust and adoption?
Pilot with 2–3 teams that depend on each other for 2–4 weeks:
- Validate the happy path (request → accept → deliver → verify/close)
- Test edge cases (reassignments, rejections, date changes)
- Iterate on required fields, status names, and alert rules
Only expand after pilot teams agree it saves time; roll out in waves with a clear “how we work now” doc linked from the app.