Apr 18, 2025·8 min
Jim Gray, Transaction Processing, and Why ACID Still Matters
A practical look at Jim Gray’s transaction processing ideas and how ACID principles keep banking, commerce, and SaaS systems reliable.
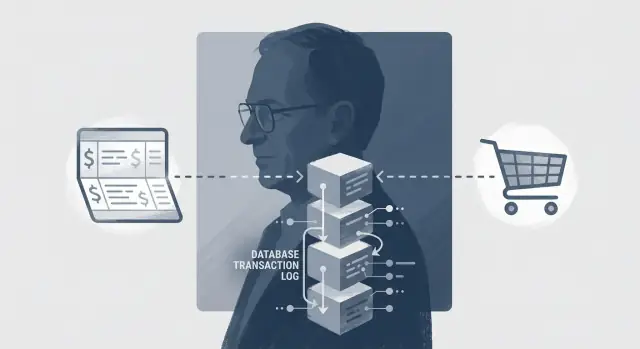
Who Jim Gray Was and Why His Ideas Persist
Jim Gray was a computer scientist who obsessed over a deceptively simple question: when lots of people use a system at the same time—and failures are inevitable—how do you keep the results right?
His work on transaction processing helped turn databases from “sometimes correct if you’re lucky” into infrastructure you can actually build a business on. The ideas he popularized—especially the ACID properties—show up everywhere, even if you’ve never used the word “transaction” in a product meeting.
What a “trustworthy system” means (in plain terms)
A trustworthy system is one where users can rely on outcomes, not just screens.
- Your bank balance doesn’t go negative because two withdrawals raced each other.
- An order is either fully placed (with inventory reserved and payment recorded) or not placed at all—no mystery limbo state.
- Subscription upgrades don’t randomly grant (or revoke) access because a background job ran twice.
- Audit logs and receipts match what actually happened, even after a crash.
In other words: correct balances, correct orders, and no missing records.
Where you’ll see Gray’s ideas in real life
Even modern products with queues, microservices, and third-party payments still depend on transaction thinking at key moments.
- Banking needs correctness over speed when money moves.
- Commerce needs safe checkout flows under load: orders, inventory, payments, refunds.
- SaaS needs consistent subscriptions, entitlements, and audit trails so customers aren’t overbilled or locked out.
What this article will do (and what it won’t)
We’ll keep the concepts practical: what ACID protects, where bugs tend to hide (isolation and concurrency), and how logs and recovery make failures survivable.
We’ll also cover modern trade-offs—where you draw ACID boundaries, when distributed transactions are worth it, and when patterns like sagas, retries, and idempotency give you “good enough” consistency without overengineering.
Transaction Processing in Plain English
A transaction is a way to treat a multi-step business action as a single “yes/no” unit. If everything succeeds, you commit it. If anything goes wrong, you roll it back as if it never happened.
A simple example: transferring money
Imagine moving $50 from Checking to Savings. That’s not one change; it’s at least two:
- Subtract $50 from Checking
- Add $50 to Savings
If your system only does “one-step updates,” it might successfully subtract the money, then fail before the deposit happens. Now the customer is missing $50—and support tickets begin.
Checkout is also more than one step
A typical checkout includes creating the order, reserving inventory, authorizing payment, and recording the receipt. Each step touches different tables (or even different services). Without transaction thinking, you can end up with an order marked “paid” but no inventory reserved—or inventory reserved for an order that was never created.
Where things fail in real life
Failures rarely happen at convenient moments. Common breakpoints include:
- The app crashes after step 1, before step 2.
- The network drops between your app and the database.
- A timeout occurs, so the user clicks “Pay” again.
- A retry or load balancer sends a duplicate request.
The goal: all steps, or none
Transaction processing exists to guarantee a simple promise: either all the steps of the business action take effect together, or none do. That promise is the foundation for trust—whether you’re moving money, placing an order, or changing a subscription plan.
ACID Refresher: What Each Letter Protects
ACID is a checklist of protections that make “a transaction” feel trustworthy. It’s not a marketing term; it’s a set of promises about what happens when you change important data.
A — Atomicity (all or nothing)
Atomicity means a transaction either completes fully or leaves no trace.
Think of a bank transfer: you debit $100 from Account A and credit $100 to Account B. If the system crashes after the debit but before the credit, atomicity ensures the whole transfer is rolled back (no one “loses” money mid-flight) or the whole transfer is completed. There is no valid end state where only one side happened.
C — Consistency (rules stay true)
Consistency means your data rules (constraints and invariants) hold after every committed transaction.
Examples: a balance can’t go negative if your product forbids overdrafts; the sum of debits and credits for a transfer must match; an order total must equal the line items plus tax. Consistency is partly a database job (constraints), and partly an application job (business rules).
I — Isolation (concurrency doesn’t corrupt results)
Isolation protects you when multiple transactions happen at the same time.
Example: two customers try to buy the last unit of an item. Without proper isolation, both checkouts might “see” inventory = 1 and both succeed, leaving inventory at -1 or forcing a messy manual correction.
D — Durability (committed means it survives)
Durability means once you see “committed,” the result won’t disappear after a crash or power loss. If the receipt says the transfer succeeded, the ledger must still show it after reboot.
A common misunderstanding
“ACID” is not a single on/off switch. Different systems and isolation levels provide different guarantees, and you often choose which protections apply to which operations.
Banking: Correctness Beats Speed When Money Moves
When people talk about “transactions,” banking is the clearest example: users expect balances to be correct, always. A banking app can be a little slow; it cannot be wrong. One incorrect balance can trigger overdraft fees, missed payments, and a long trail of follow-up work.
One transfer, one unit of work
A simple bank transfer isn’t one action—it’s several that must succeed or fail together:
- Debit account A.
- Credit account B.
- Write an audit record (who/when/why/how much).
ACID thinking treats that as a single unit. If any step fails—network hiccup, service crash, validation error—the system must not “partially succeed.” Otherwise, you get money missing from A but not showing up in B, money in B without a matching debit, or no audit trail to explain what happened.
Why “we’ll fix it later” gets expensive
In many products, a small inconsistency can be patched in the next release. In banking, “eventual fix later” turns into disputes, regulatory exposure, and manual operations. Support tickets spike, engineers are pulled into incident calls, and operations teams spend hours reconciling mismatched records.
Even if you can correct the numbers, you still need to explain the history.
Ledgers, immutable logs, and reconciliation
That’s why banks rely on ledgers and append-only records: instead of overwriting history, they record a sequence of debits and credits that add up. Immutable logs and clear audit trails make recovery and investigation possible.
Reconciliation—comparing independent sources of truth—acts as a backstop when something goes wrong, helping teams pinpoint when and where a divergence occurred.
The user impact
Correctness buys trust. It also reduces support volume and speeds resolution: when a problem does occur, a clean audit trail and consistent ledger entries mean you can answer “what happened?” quickly, and fix it without guesswork.
Commerce: Orders, Inventory, and Payments Under Load
E-commerce feels simple until you hit peak traffic: the same last item is in ten carts, customers refresh the page, and your payment provider times out. This is where Jim Gray’s transaction-processing mindset shows up in practical, unglamorous ways.
A checkout, broken into steps
A typical checkout touches multiple pieces of state: reserve inventory, create the order, and capture payment. Under heavy concurrency, each step can be correct on its own yet still produce a bad overall outcome.
If you decrement inventory without isolation, two checkouts can read “1 left” and both succeed—hello overselling. If you capture payment and then fail to create the order, you’ve charged a customer with nothing to fulfill.
ACID helps most at the database boundary: wrap the order creation and inventory reservation in a single database transaction so they either both commit or both roll back. You can also enforce correctness with constraints (for example, “inventory can’t go below zero”) so the database rejects impossible states even when application code misbehaves.
Payments: why “exactly once” is hard
Networks drop responses, users double-click, and background jobs retry. That’s why “exactly once” processing is difficult across systems. The goal becomes: at most once for money movement, and safe retries everywhere else.
Use idempotency keys with your payment processor and store a durable record of “payment intent” tied to your order. Even if your service retries, you don’t double-charge.
Refunds and chargebacks
Returns, partial refunds, and chargebacks are business facts, not edge cases. Clear transaction boundaries make them easier: you can reliably link every adjustment to an order, a payment, and an audit trail—so reconciliation is explainable when something goes wrong.
SaaS: Subscriptions, Entitlements, and Audit Trails
Keep ownership of your build
Get full source code export so your team can review, extend, and productionize the result.
SaaS businesses live on a promise: what the customer pays for is what they can use, immediately and predictably. That sounds simple until you mix plan upgrades, downgrades, mid-cycle proration, refunds, and asynchronous payment events. ACID-style thinking helps keep “billing truth” and “product truth” aligned.
Subscription changes without surprises
A plan change often triggers a chain of actions: create or adjust an invoice, record proration, collect payment (or attempt it), and update entitlements (features, seats, limits). Treat these as a single unit of work where partial success is unacceptable.
If an upgrade invoice is created but entitlements aren’t updated (or vice versa), customers either lose access they paid for or get access they didn’t.
A practical pattern is to persist the billing decision (new plan, effective date, proration lines) and the entitlement decision together, then run downstream processes off that committed record. If payment confirmation arrives later, you can move state forward safely without rewriting history.
Multi-tenant correctness
In multi-tenant systems, isolation isn’t academic: one customer’s heavy activity must not block or corrupt another’s. Use tenant-scoped keys, clear transaction boundaries per tenant, and carefully chosen isolation levels so a burst of renewals for Tenant A doesn’t create inconsistent reads for Tenant B.
Audit trails that answer support questions
Support tickets usually start with “Why was I charged?” or “Why can’t I access X?” Maintain an append-only audit log of who changed what and when (user, admin, automation), and tie it to invoices and entitlement transitions.
This prevents silent drift—where invoices say “Pro” but entitlements still reflect “Basic”—and makes reconciliation a query, not an investigation.
Isolation and Concurrency: Where Most Bugs Hide
Isolation is the “I” in ACID, and it’s where systems often fail in subtle, expensive ways. The core idea is simple: many users act at once, but each transaction should behave as if it ran alone.
An everyday analogy: two cashiers, one item
Imagine a store with two cashiers and one last item on the shelf. If both cashiers check stock at the same time and both see “1 available,” they might each sell it. Nothing “crashed,” but the outcome is wrong—like a double-spend.
Databases face the same problem when two transactions read and update the same rows concurrently.
Common anomalies isolation is meant to prevent
- Dirty reads: you see changes from a transaction that hasn’t committed yet (and might roll back).
- Lost updates: two transactions update the same record, and the later write silently overwrites the earlier one.
- Double-spend-style bugs: two transactions both “reserve” the same scarce resource (inventory, balance, seats).
Isolation levels in plain terms
Most systems choose an isolation level as a tradeoff between safety and throughput:
- Read committed: only reads committed data. Helps avoid dirty reads, but some anomalies can still slip through.
- Repeatable read: ensures that if you re-read the same row, you get the same result. Reduces “moving target” behavior, but not every kind of conflict.
- Serializable: the strongest—results are as if transactions ran one-by-one. Safest, but often slowest.
Choose based on business risk, not only performance
If a mistake creates financial loss, legal exposure, or customer-visible inconsistency, lean toward stronger isolation (or explicit locking/constraints). If the worst case is a temporary UI glitch, a weaker level might be acceptable.
Higher isolation can reduce throughput because the database must do more coordination—waiting, locking, or aborting/retrying transactions—to prevent unsafe interleavings. The cost is real, but so is the cost of incorrect data.
Logs, Durability, and Recovery After Failures
Add idempotency by design
Have Koder.ai scaffold idempotency keys, dedupe tables, and unique constraints for risky actions.
When a system crashes, the most important question isn’t “why did it crash?” but “what state should we be in after restart?” Jim Gray’s transaction processing work made the answer practical: durability is achieved through disciplined logging and recovery.
The transaction log: the system’s memory
A transaction log (often called the WAL) is an append-only record of changes. It’s central to recovery because it preserves the intent and order of updates even if the database files are mid-write when power dies.
During restart, the database can:
- Redo committed changes that didn’t fully reach data files.
- Undo incomplete transactions so half-finished updates don’t leak into the final state.
This is why “we committed it” can remain true even when the server didn’t shut down cleanly.
Write-ahead logging (WAL) and why it enables durability
Write-ahead logging means: the log is flushed to durable storage before the data pages are allowed to be written. In practice, “commit” is tied to ensuring the relevant log records are safely on disk (or otherwise durable).
If a crash happens right after commit, recovery can replay the log and reconstruct the committed state. If the crash happens before commit, the log helps roll back.
Backups vs logs: you want both
A backup is a snapshot (a point-in-time copy). Logs are a history (what changed after that snapshot). Backups help with catastrophic loss (bad deploy, dropped table, ransomware). Logs help you recover recent committed work and can support point-in-time recovery: restore the backup, then replay logs up to a chosen moment.
Operational reminder: test restores
A backup you’ve never restored is a hope, not a plan. Schedule regular restore drills into a staging environment, verify data integrity checks, and time how long recovery actually takes. If it doesn’t meet your RTO/RPO needs, adjust retention, log shipping, or backup cadence before an incident forces the lesson.
Distributed Systems: ACID Boundaries and Practical Alternatives
ACID works best when one database can act as the “source of truth” for a transaction. The moment you spread one business action across multiple services (payments, inventory, email, analytics), you enter distributed systems territory—where failures don’t look like clean “success” or “error.”
Why distributed transactions are hard
In a distributed setup, you must assume partial failures: one service might commit while another crashes, or a network hiccup might hide the true outcome. Even worse, timeouts are ambiguous—did the other side fail, or is it just slow?
That uncertainty is where double-charges, overselling, and missing entitlements are born.
Two-phase commit (2PC) in plain terms
Two-phase commit tries to make multiple databases commit “as one.”
- Phase 1 (prepare): each participant promises it can commit and locks what it needs.
- Phase 2 (commit/abort): a coordinator tells everyone to finalize, or to roll back.
Teams often avoid 2PC because it can be slow, it holds locks longer (hurting throughput), and the coordinator can become a bottleneck. It also couples systems tightly: all participants must speak the protocol and stay highly available.
Practical alternatives that scale better
A common approach is to keep ACID boundaries small and manage cross-service work explicitly:
- Sagas: split a big process into steps, each with its own local transaction.
- Compensating actions: if step 4 fails, run “undo” steps (refund payment, release inventory).
- Outbox pattern: write your database change and the “event to publish” in the same local transaction, then reliably send it later.
Rule of thumb
Put the strongest guarantees (ACID) inside a single database whenever possible, and treat everything beyond that boundary as coordination with retries, reconciliation, and clear “what happens if this step fails?” behavior.
Retries, Idempotency, and Duplicate Requests
Failures rarely look like clean “it didn’t happen.” More often, a request partially succeeds, the client times out, and someone (a browser, mobile app, job runner, or partner system) retries.
Without safeguards, retries create the nastiest kind of bug: correct-looking code that occasionally double-charges, double-ships, or double-grants access.
What idempotency means (in practice)
Idempotency is the property that performing the same operation multiple times has the same end result as performing it once. For user-facing systems, it’s “safe retries without double effects.”
A helpful rule: GET should be naturally idempotent; many POST actions are not unless you design them to be.
Tools that prevent duplicates
You typically combine a few mechanisms:
- Idempotency keys: the client sends a unique key per intended action (e.g.,
Idempotency-Key: ...). The server stores the outcome keyed by that value and returns the same result on repeats. - Unique constraints: enforce “only one” at the database level (e.g., one payment per
order_id, one subscription peraccount_id + plan_id). - Deduplication tables: store processed request IDs/events (common for webhooks and message queues), often with a TTL.
These work best when the unique check and the effect live in the same database transaction.
Retries vs. transactions and timeouts
A timeout doesn’t mean the transaction rolled back; it may have committed but the response got lost. That’s why retry logic must assume the server could have succeeded.
A common pattern is: write an idempotency record first (or lock it), perform the side effects, then mark it complete—all within a transaction when possible. If you can’t fit everything in one transaction (for example, calling a payment gateway), persist a durable “intent” and reconcile later.
Everyday examples
- Double-click “Submit payment”: two identical requests arrive. Without idempotency, you risk two charges.
- Webhook redelivery: providers resend events until acknowledged. Without dedupe, you may create duplicate invoices or provision access twice.
Design and Test Checklist for Trustworthy Data
Plan transaction boundaries first
Use Planning Mode to map transaction boundaries and invariants before you generate code.
When systems “feel flaky,” the root cause is often broken transaction thinking. Typical symptoms include phantom orders that appear without a corresponding payment, negative inventory after concurrent checkouts, and mismatched totals where the ledger, invoices, and analytics don’t agree.
Design checklist (before you write code)
Start by writing down your invariants—the facts that must always be true. Examples: “inventory never drops below zero,” “an order is either unpaid or paid (not both),” “every balance change has a matching ledger entry.”
Then define transaction boundaries around the smallest unit that must be atomic to protect those invariants. If a single user action touches multiple rows/tables, decide what must commit together and what can be safely deferred.
Finally, choose how you’ll handle conflicts under load:
- Locking vs. optimistic concurrency (version columns).
- Unique constraints to prevent duplicates (e.g., one payment per order).
- Clear retry rules when deadlocks/timeouts happen.
Testing ideas that catch real-world failures
Concurrency bugs rarely show up in happy-path tests. Add tests that create pressure:
- Concurrency tests: run the same operation from many threads/processes; assert invariants after completion.
- Fault injection: kill the service mid-transaction, drop DB connections, or force timeouts; verify recovery leaves no half-finished state.
- Replay production-like traffic: reuse request sequences (sanitized) to reproduce edge cases and validate fixes.
Monitoring signals worth alerting on
You can’t protect what you don’t measure. Useful signals include deadlocks, lock wait time, rollback rates (especially spikes after deploys), and reconciliation diffs between source-of-truth tables (ledger vs. balances, orders vs. payments). These metrics often warn you weeks before customers report “missing” money or inventory.
How to Apply ACID Thinking Without Overengineering
Jim Gray’s lasting contribution wasn’t just a set of properties—it was a shared vocabulary for “what must not go wrong.” When teams can name the guarantee they need (atomicity, consistency, isolation, durability), debates about correctness stop being vague (“it should be reliable”) and become actionable (“this update must be atomic with that charge”).
Where to insist on ACID
Use full transactions when a user would reasonably expect a single, definitive outcome and mistakes are costly:
- Money movement: charges, refunds, balance updates, payouts.
- Order commitment: creating an order + reserving inventory + recording payment intent.
- Access and entitlements: subscription changes, role grants, license seats.
- Audit requirements: anything you must explain later to a customer, finance, or security.
Here, optimizing for throughput by weakening guarantees often just shifts cost into support tickets, manual reconciliation, and lost trust.
Where weaker guarantees are fine
Relax guarantees when temporary inconsistency is acceptable and easy to heal:
- Read models and analytics (minutes-late reporting is usually fine).
- Non-critical counters (views, likes) where duplicates don’t matter.
- Async side effects (emails, webhooks) as long as they’re idempotent.
The trick is to keep a clear ACID boundary around the “source of truth,” and let everything else lag behind.
Practical next steps (lightweight, high impact)
- List your critical flows: money, orders, access, and anything that changes a contract with the customer.
- Write invariants in plain English (and keep them near the code): “An order is paid at most once,” “A seat can’t be assigned twice,” “Balance never goes negative.”
- Map each invariant to a mechanism: transaction scope, unique constraints, idempotency keys, append-only audit log.
- Test the ugly paths: retries, timeouts, double-clicks, and partial failures.
If you’re prototyping these flows (or rebuilding a legacy pipeline), it helps to start from a stack that makes transactions and constraints first-class. For example, Koder.ai can generate a React front end plus a Go + PostgreSQL backend from a simple chat, which is a practical way to stand up “real” transaction boundaries early (including idempotency records, outbox tables, and rollback-safe workflows) before you invest in a full microservices rollout.
If you want more patterns and checklists, link these expectations from /blog. If you offer reliability expectations by tier, make them explicit on /pricing so customers know what correctness guarantees they’re buying.
FAQ
Who was Jim Gray, and why do his ideas still matter?
Jim Gray was a computer scientist who helped make transaction processing practical and widely understood. His legacy is the mindset that important multi-step actions (money movement, checkout, subscription changes) must produce correct outcomes even under concurrency and failures.
In day-to-day product terms: fewer “mystery states,” fewer reconciliation fires, and clearer guarantees about what committed really means.
What is a transaction in plain English?
A transaction groups multiple updates into a single all-or-nothing unit. You commit when all steps succeed; you roll back when anything fails.
Typical fits:
- Bank transfer: debit + credit + audit record
- Checkout: create order + reserve inventory
- Subscription change: billing decision + entitlement change
What do the ACID properties actually protect?
ACID is a set of guarantees that make transactions trustworthy:
- Atomicity: all steps happen, or none do
- Consistency: rules/invariants stay true after commit
- Isolation: concurrent activity doesn’t produce incorrect results
- Durability: committed results survive crashes
It’s not a single switch—you choose where you need these guarantees and how strong they must be.
Why is isolation the source of so many concurrency bugs?
Most “it only happens in production” bugs come from weak isolation under load.
Common failure patterns:
- Lost updates: two writers overwrite each other
- Double-spend/oversell: two checkouts reserve the same last unit
- Dirty reads: seeing data from a transaction that later rolls back
Practical fix: pick an isolation level based on business risk, and backstop it with constraints/locking where needed.
How do I define invariants and choose good transaction boundaries?
Start by writing invariants in plain English (what must always be true), then enforce them in the smallest possible transaction scope.
Mechanisms that work well together:
- Database constraints (e.g., “inventory can’t go below zero”)
- Unique constraints (e.g., “one payment per order”)
- Optimistic concurrency (version columns) or explicit locks
Treat constraints as a safety net for when application code gets concurrency wrong.
What are WAL and the transaction log, and why do they matter?
Write-ahead logging (WAL) is how databases make “commit” survive crashes.
Operationally:
- The DB appends changes to an append-only log
- On restart it can redo committed work and undo incomplete work
This is why a clean design can be: if it committed, it stays committed, even after power loss.
Do I need backups if I already have transaction logs (or WAL)?
Backups are point-in-time snapshots; logs are the history of changes since that snapshot.
A practical recovery posture is:
- Take periodic backups
- Retain/ship logs for point-in-time recovery
- Regularly test restores in staging and measure real RTO/RPO
If you’ve never restored from it, it’s not a plan yet.
Why are distributed transactions (like 2PC) often avoided?
Distributed transactions try to make multiple systems commit as one, but partial failures and ambiguous timeouts make this hard.
Two-phase commit (2PC) typically adds:
- Long-held locks (throughput hit)
- Tight coupling between services
- Coordinator bottlenecks and availability concerns
Use it when you truly need cross-system atomicity and can afford the operational complexity.
What are practical alternatives to distributed ACID across services?
Prefer small local ACID boundaries and explicit coordination between services.
Common patterns:
- Sagas: break a workflow into steps with local transactions
- Compensating actions: refund/release/revoke when later steps fail
- Outbox pattern: write DB change + event-to-publish in one transaction, then publish reliably
This gives predictable behavior under retries and failures without turning every workflow into a global lock.
How do retries and idempotency prevent double-charges and duplicate orders?
Assume a timeout might mean “it succeeded but you didn’t hear back.” Design retries to be safe.
Tools that prevent duplicates:
- Idempotency keys for user actions and payments
- Unique constraints to enforce “at most one” effects
- Dedupe tables for webhooks/events (often with TTL)
Best practice: keep the dedupe check and the state change in the same database transaction whenever possible.